
The transition from a successful prototype to a production-ready autonomous agent represents one of the most significant architectural hurdles facing modern IT departments in 2026. While a demo often impresses stakeholders with its conversational fluidity and rapid task execution, the operational

The silent engine of modern software development hums within the automated lines of CI/CD pipelines, yet this very speed often masks a catastrophic vulnerability lurking in the shadows of plain-text credentials. In the contemporary DevOps landscape, Continuous Integration and Continuous Deployment

The transition from a flashy social media demonstration to a fully operational, enterprise-grade AI agent represents the single most significant hurdle for software engineers in the current technological landscape. While it has become trivial to string together a few API calls to create a bot that

The modern software factory no longer operates within the safety of a guarded server room but instead relies on a sprawling, interconnected web of global dependencies that effectively dissolves the traditional perimeter. As development cycles have compressed to meet the demands of an always-on

A sudden, unexplained fluctuation in a regional power grid or a localized disruption in an emergency response network can ripple through a community with devastating speed, highlighting the precarious nature of modern infrastructure. Control rooms serve as the nerve centers for these essential
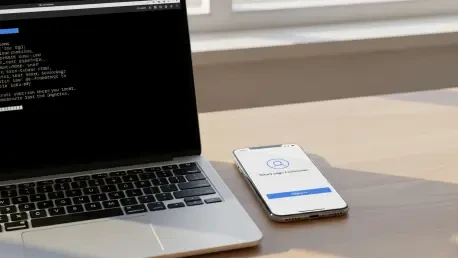
Modern application ecosystems frequently require secure authentication on hardware that lacks a standard keyboard or a full-featured web browser, creating a significant friction point for users who just want to get work done. Imagine the frustration of a developer attempting to log into a cloud