Rapid CI/CD pipelines now pull images, spin up containers, call external APIs, seed databases, and knit together dozens of services, and every one of those actions depends on credentials that are too easy to mishandle when speed outruns security. That tension has pushed secrets management from a background utility into a frontline control for software delivery, especially as microservices shift state and configuration into environment variables, sidecars, and runtime requests. Failure patterns are stubbornly consistent: hardcoded API keys in GitHub repos, long-lived tokens hiding in Terraform state, shared passwords riding around Slack, and pipelines that echo secrets into logs. Attackers do not need novel exploits when a dangling key opens the door to production. The response is equally pragmatic: centralize secrets, broker access through identity, automate rotation, and make every retrieval observable. Done well, development accelerates because credentials stop being a manual chore and start being a predictable service.
The Stakes: Why Secrets Management Defines Modern Delivery
Modern delivery stacks favor composability: Kubernetes orchestrates workloads, GitHub Actions or GitLab CI chains steps, Argo CD and Flux handle GitOps, and IaC tools such as Terraform or Pulumi stamp infrastructure across regions. In this web, secrets multiply quickly. A single service might need a database password, a payment gateway token, an S3 key, and a message broker credential, all varying by environment. Sprinkle in OpenID Connect federation for cloud access and identity sprawl expands further. Breaches frequently trace to small oversights—an unrotated token with admin scope or a leaked .env file. The cost is not only intrusion; it is also lost time chasing provenance and revoking access under fire. Organizations that routinized secret hygiene discovered that guardrails reduced friction rather than adding it, because engineers no longer improvised.
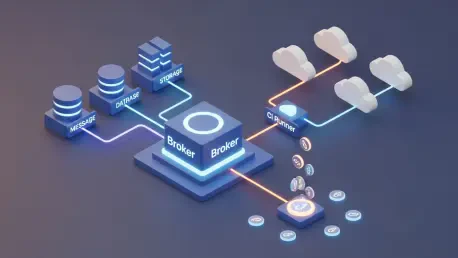
A dedicated secrets manager changes the pattern by removing static credentials from code and replacing them with on-demand retrieval. Applications authenticate using machine identities—Kubernetes service accounts, cloud instance metadata, or OIDC-issued JWTs—and the manager issues time-bound secrets through a secure channel. Databases gain user-per-request accounts that expire in minutes, SSH logins become just-in-time certificates, and pipeline jobs receive ephemeral tokens bound to workload identity instead of pre-shared strings. Each read is logged with who, what, when, and where, funneling into SIEM pipelines for anomaly detection. Rotation policies run continuously, cutting blast radius if a key escapes. In practice, this looks like sidecar or CSI driver mounts in Kubernetes, native actions in GitHub, or plugin steps in Jenkins that fetch credentials at runtime, keeping logs and artifacts clean while preserving least privilege.
Choosing Capabilities and Platforms: From CI/CD Fit to Multi-Cloud Reach
Capability priorities tend to align across high-performing teams. First, centralization matters because secrets scattered across S3 buckets, GitLab variables, and VM files drift out of sync. A single encrypted store, backed by hardware-rooted keys or cloud KMS, anchors policy and lifecycle. Next, dynamic secrets curb standing privileges: per-connection Postgres users, short-lived cloud credentials minted via STS or workload identity, and ephemeral TLS or SSH certs reduce exposure dramatically. Automation completes the picture—rotation schedules, revocation hooks, and drift detection prevent stale access. Integrations must be first-class: GitHub Actions OIDC, GitLab JWTs, Jenkins credentials bindings, Kubernetes CSI driver, Lambda and Cloud Run environment injection, and Terraform providers that never embed cleartext. Finally, audit depth is non-negotiable; per-tenant logs with immutable storage and SIEM exports underpin compliance and incident response.
Vendor choices reflect trade-offs between control, scope, and operational load. HashiCorp Vault remains the archetype for flexibility, with mountable engines for databases, PKI, and cloud credentials, plus policy written in HCL and Sentinel; it excels in organizations with platform engineering maturity ready to operate HA clusters and unseal workflows. Akeyless brings a SaaS control plane designed for hybrid estates, using distributed fragments and identity-based access to reach on-prem and multi-cloud without standing up clusters; breadth of integration is strong, though complex estates benefit from careful initial modeling. Cloud-native options—the trio of AWS Secrets Manager, Azure Key Vault, and Google Secret Manager—integrate tightly with IAM, serverless runtimes, and managed databases; they simplify single-cloud shops but grow awkward across providers and can lack advanced dynamic engines outside their ecosystems. Selection, therefore, hinges on cloud footprint, appetite for operations, and how far automation needs to go.
What Comes Next: Trends, DevOps Impact, and Practical Selection Steps
Several trends have been reshaping the baseline. Security shifted left into developer workflows using pre-commit scanners, policy checks in CI, and GitOps admission controls that reject hardcoded secrets. Dynamic, ephemeral credentials became the default for sensitive paths: cloud access through OIDC federation to AWS STS or Google Workload Identity, database accounts minted per job, and short-lived signing keys issued by an internal CA. Identity consolidation matured as platforms tied roles to workloads, not humans alone, with SPIFFE/SPIRE and cloud-native attestation reinforcing provenance. Tooling also normalized: Kubernetes operators and CSI drivers mount secrets securely, while policy engines like OPA and Kyverno enforce least privilege. Observability strengthened through structured audit logs streamed to Splunk or Elastic with correlation IDs that bind events to git SHAs and pipeline runs, closing the loop from commit to credential use.
Executed well, secrets management sped delivery rather than slowing it. By injecting credentials at runtime, GitHub Actions stopped persisting long-lived tokens, Jenkins cleaned up credential wrappers, and Helm or Kustomize stopped templating secrets into manifests. Developers no longer passed tokens through chat or copied .env files between laptops, and break-glass procedures shrank to automated revocation and reissue. Human error dropped as credentials rotated transparently under policy, while compliance benefited from deterministic evidence trails. The practical path forward started with a discovery phase that enumerated secret flows per service, mapped identities used in CI and runtime, and cataloged stores currently in play. Pilots then validated dynamic secrets for a high-impact target—often the primary database or cloud accounts—before expanding to pipelines and third-party integrations like Stripe or Twilio, proving value early.
The concluding steps had to be concrete and time-bound. Teams established workload identity as the default, replacing shared keys with OIDC or SPIFFE wherever supported. Policy shifted to least privilege with deny-by-default, codified as versioned policy alongside application code, and enforced by admission controllers. Rotation windows were shortened to hours or minutes for high-value targets, with alerts on deviation and automatic quarantine for noncompliant workloads. Backups and disaster recovery incorporated escrowed root material and tested unseal or failover procedures, preventing control-plane fragility. Finally, procurement and architecture decisions prioritized platforms that matched the operating model: cloud-native stores for single-cloud stacks, cross-cloud SaaS for hybrid reach, or self-managed Vault where customization justified the lift. Following this playbook, secrets management raised the security floor and kept delivery fast, predictable, and auditable.