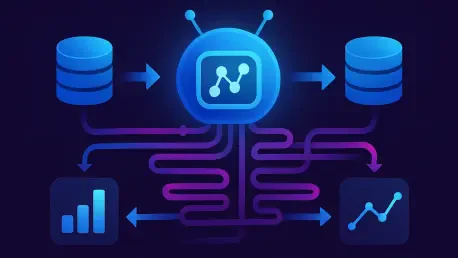
The transformation of the modern enterprise hinges no longer on the sheer volume of information collected but on the precision with which that data is curated and deployed by autonomous systems. The agentic data pipelines represent a significant advancement in the data engineering and artificial
Software developers frequently encounter the frustrating bottleneck of empty database tables when trying to validate complex queries or optimize system performance before a major production launch. Without a substantial volume of information, even the most elegantly designed application can fail to

The rapid evolution of cloud-native infrastructure in 2026 has placed an unprecedented premium on code maintainability and architectural flexibility, yet many development teams still struggle with the "complexity wall" that emerges as Go projects scale. While the language was designed to promote
The rapid transition from passive language models to proactive autonomous agents has forced a fundamental architectural reckoning regarding the balance between control and utility in the year 2026. As artificial intelligence moves beyond simple conversational interfaces into the realm of agentic
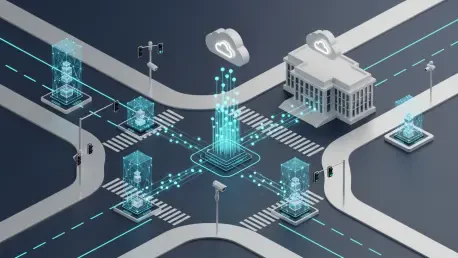
The administrative burden of processing nearly forty thousand citizen safety reports every single day has historically pushed public infrastructure to its absolute limit, often resulting in delayed responses during critical emergencies. To address these systemic bottlenecks, LG AI Research and the

Enterprises today frequently find themselves trapped in a cycle where adding more technology results in less efficiency, creating a paradox that undermines the very goal of digital transformation. While the promise of automation suggests a future of streamlined operations and reduced manual labor,