
The modern technological landscape is currently undergoing a fundamental transformation as digital interaction matures from passive, response-driven chatbots into a new era of fully autonomous AI agents designed to execute complex workflows without human oversight. These "agentic" systems represent

The recent disclosure of two maximum-severity vulnerabilities within the Cisco Secure Firewall Management Center represents a watershed moment for enterprise network administrators who rely on centralized orchestration for their defense-in-depth strategies. These flaws, specifically tracked as

The rapid integration of autonomous artificial intelligence into corporate infrastructure has reached a point where digital agents now possess the authority to execute complex system-level tasks without constant human oversight. This shift toward autonomy has introduced a sophisticated class of

Modern infrastructure management frequently demands a delicate balance between local control and cloud-scale efficiency, leading many technical professionals to seek sandboxed environments that mimic production settings without the massive overhead of specialized hardware. The emergence of
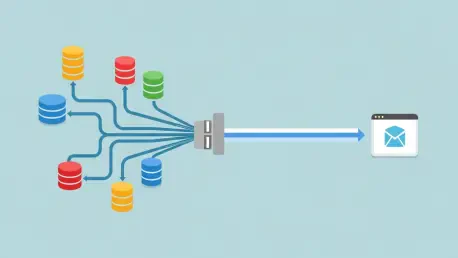
The modern enterprise data landscape is a sprawling, complex ecosystem where monolithic relational databases now share the stage with a diverse cast of NoSQL solutions, creating a fragmented and challenging environment for developers. This reality has catalyzed a strategic shift toward unified data
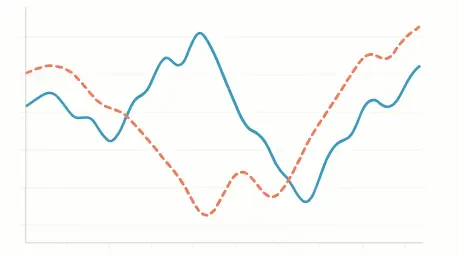
While the principle of randomization stands as the undisputed cornerstone of modern A/B testing, a subtle yet potent threat can systematically dismantle the integrity of an experiment long after users have been neatly sorted into control and treatment groups. This insidious problem, known as