

The modern enterprise attack surface has expanded so rapidly that traditional point solutions can no longer keep pace with the sophisticated, multi-layered strategies employed by contemporary threat actors. As organizations integrate complex generative AI models and sprawling third-party API
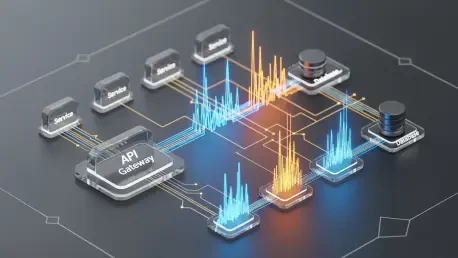
Modern microservices architectures often resemble a digital labyrinth where a single user action triggers a cascade of events across dozens of isolated systems. In such an environment, the moment a database starts lagging or a message broker becomes congested, engineers frequently find themselves

The persistent tension between rapid software delivery and rigorous security compliance has reached a critical inflection point within modern engineering teams. As the complexity of the JavaScript and TypeScript ecosystems continues to expand, developers often find themselves overwhelmed by the

The staggering reality of modern software operations is that high-value senior engineers currently sacrifice up to forty percent of their creative output to the exhausting, manual labor of reconstructing failure timelines during system outages. This systemic inefficiency represents a hidden tax on

Achieving structural integrity in massive 3D-printed components often involves a costly cycle of trial and error that drains resources and stalls industrial production timelines. This systemic inefficiency has long plagued the additive manufacturing sector, where the sheer scale of parts makes
Vijay Raina is a seasoned authority in enterprise SaaS technology and a visionary in software architecture, specifically known for his work in optimizing the complex lifecycles of AI-driven applications. Recently, he has focused on the critical intersection of Retrieval-Augmented Generation (RAG)

The global landscape of administrative governance is currently witnessing a profound shift as metropolitan centers seek to replace traditional, reactive bureaucracy with intelligent systems capable of anticipating the needs of a mobile population. In Dubai, this evolution has reached a critical

Regulators on both sides of the Atlantic are significantly intensifying their enforcement actions, creating a precarious environment for any organization handling sensitive health and personal information. Hospitals throughout Europe now face the reality of multimillion-euro GDPR fines resulting

The persistent struggle to synchronize massive enterprise teams has finally met its match in a sophisticated technological triad that replaces human guesswork with algorithmic precision. This evolution represents a departure from the traditional Scaled Agile Framework (SAFe), which often buckled

In the rapidly evolving landscape of enterprise software, the ability to bridge the gap between natural language and complex database queries is becoming a cornerstone of modern SaaS architecture. Vijay Raina, a seasoned specialist in enterprise technology and software design, has spent a
ITCurated uses cookies to personalize your experience on our website. By continuing to use this site, you agree to our Cookie Policy