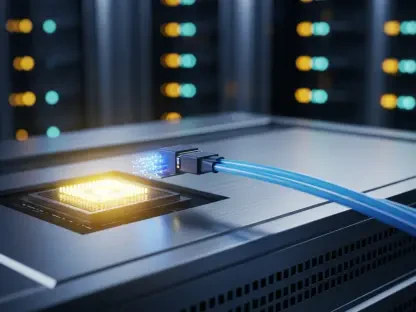
The recent federal intervention against the Handala cyber espionage group underscores the escalating severity of state-sponsored digital warfare and its direct impact on global healthcare infrastructure. By seizing critical digital infrastructure, federal law enforcement agencies successfully neutralized several command domains, including Handala-Hack and Handala-Redwanted, effectively displaying official seizure notices where propaganda once lived. This decisive action followed a catastrophic breach of the medical technology titan Stryker, an organization with a presence in dozens of nations. During this intrusion, the threat actors reportedly exfiltrated a staggering 50 terabytes of sensitive data and deployed destructive wiper malware that paralyzed over 200,000 systems. While the company maintains extensive operations worldwide, the breach caused significant operational friction within its primary innovation hubs in Ireland. The scale of this disruption highlights the vulnerability of even the most sophisticated corporations when targeted by focused espionage campaigns.
Tactical Evolution: Sophisticated Toolsets and Intune Exploitation
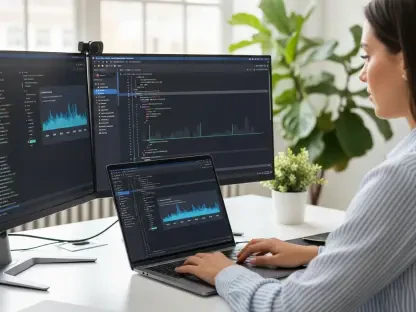
Technical investigations conducted by cybersecurity researchers at Cisco Talos and Splunk revealed that Handala is a highly capable “hacktivist” entity that has been refining its methodology since late 2023. The group did not rely solely on simple exploits but instead utilized a multifaceted approach that combined high-pressure phishing extortion with the deployment of bespoke wiper malware compatible with both Windows and Linux environments. A particularly alarming aspect of their campaign involved the exploitation of Microsoft Intune, a cloud-based endpoint management solution, to facilitate the widespread delivery of their destructive payloads. By compromising administrative access within the device management ecosystem, the actors were able to bypass traditional perimeter defenses and execute system-wide deletions with high efficiency. This methodology demonstrated a deep understanding of corporate IT administration, allowing the group to turn legitimate management tools against the very organizations they were designed to protect from external threats.
Strategic Defenses: Hardening Systems Against Future Incursions
In response to these pervasive threats, the Cybersecurity and Infrastructure Security Agency prioritized the dissemination of advanced hardening guidelines for all organizations utilizing cloud-based endpoint management. Security experts emphasized that the most effective deterrent involved the rigorous implementation of a least-privilege architecture for all administrative roles. It became clear that enforcing phishing-resistant multi-factor authentication served as a critical barrier against the credential harvesting techniques favored by Iranian-linked actors. Furthermore, the integration of Multi Admin Approval protocols within software like Microsoft Intune ensured that no single compromised account could authorize large-scale environmental changes. These defensive adjustments provided a necessary layer of verification that mitigated the risk of unauthorized system-wide wipes. Ultimately, the coordinated effort between law enforcement and technical advisors established a blueprint for resilient privileged access hygiene, ensuring that enterprises remained better prepared for the persistent challenges of modern cyber espionage.