
The pressure to deliver artificial intelligence capabilities often leads engineering teams to prioritize rapid feature deployment over the long-term stability of their production environments. While the allure of generative AI is undeniable, the reality of integrating these non-deterministic
The rapid decentralization of organizational assets has rendered traditional, script-reliant endpoint management methods insufficient for the complexities of a hyper-connected global enterprise. For decades, the primary goal of the information technology department was to maintain a stable
Every growing enterprise eventually hits a wall where the simple act of generating a personalized PDF becomes a massive operational anchor. It usually starts small, with an administrative assistant manually pulling a client name from a CRM and pasting it into a Word template, but as the volume of
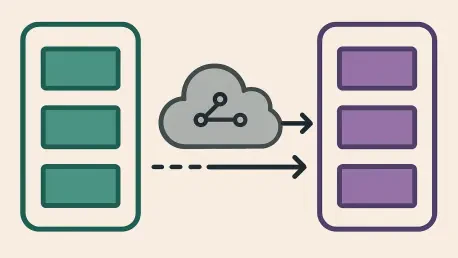
Modernizing legacy architectural frameworks is often compared to performing an engine swap on a vehicle while it is cruising down the highway at seventy miles per hour without ever tapping the brakes. The inherent complexity of distributed systems, combined with the pressure to maintain constant

As an expert in enterprise SaaS technology and software architecture, Vijay Raina has spent years navigating the intricate plumbing of the internet. With a deep background in designing resilient cloud infrastructures, he has witnessed firsthand how a simple misunderstanding of core protocols can

The rapid transformation of the Middle East into a global fintech powerhouse has reached a critical inflection point, as Dubai and Abu Dhabi now command a significant share of the international foreign exchange market through sophisticated digital infrastructure. As of 2026, the United Arab
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24