The persistent myth that a perfect firewall or a rigorous annual audit can safeguard a complex Java ecosystem has been shattered by a reality where vulnerabilities are discovered faster than they can be patched. For decades, the enterprise sector relied on exhaustive, checklist-driven compliance that treated every line of code and every third-party library with equal suspicion, leading to “security fatigue” and stalled deployments. The Risk-Driven Enterprise Java Security framework emerges as a necessary departure from this binary mindset, advocating for a surgical approach that aligns technical defense with actual business impact. By shifting the focus from total prevention to prioritized risk management, this framework addresses the fundamental bottleneck in modern DevSecOps: the inability to fix everything at once.
Evolution of Risk-Based Architecture in Java Ecosystems
The Java ecosystem has transitioned from a collection of monolithic applications to a sprawling web of microservices, cloud-native APIs, and deep dependency trees. In the past, security was often an afterthought, bolted onto the application just before production through a series of rigid gateway checks. However, as the frequency of supply chain attacks increased, the industry realized that a flat security model—where an internal utility library receives the same scrutiny as a public-facing authentication gateway—was both inefficient and dangerous. This realization birthed the risk-driven architecture, a methodology that integrates security directly into the design phase of the software development lifecycle.
The core principle behind this evolution is the transition from reactive patching to proactive posture management. Instead of waiting for a vulnerability scanner to flag thousands of issues, organizations now use risk-based logic to determine which vulnerabilities actually pose a threat to their specific environment. This context-aware approach ensures that developers spend their limited time securing high-traffic entry points and sensitive data stores rather than chasing low-impact bugs in isolated modules. In the broader technological landscape, this shift represents the maturation of “Security as Code,” where defense is no longer a barrier to speed but a component of software quality.
Core Pillars of Risk-Driven Java Security
Strategic Risk Prioritization Logic
At the heart of this framework lies a sophisticated risk matrix that evaluates potential threats based on likelihood, impact, and exposure. While traditional models often rely solely on the Common Vulnerability Scoring System (CVSS), a risk-driven approach adds a layer of business intelligence. It asks whether a component supports revenue-generating services or handles identity management, effectively weighing the cost of a breach against the cost of mitigation. This logic prevents the common pitfall of “security theater,” where teams appear busy but fail to move the needle on actual enterprise safety.
Practical Threat Modeling via STRIDE
Rather than treating threat modeling as a high-level academic exercise, the framework employs the STRIDE methodology—Spoofing, Tampering, Repudiation, Information Disclosure, Denial of Service, and Elevation of Privilege—directly at the API level. For instance, when reviewing a Java REST API, the system identifies missing audit logs for privileged actions as a repudiation risk or unthrottled endpoints as a denial-of-service vulnerability. This granular analysis allows architects to implement specific mitigations, such as rate limiting or enhanced token validation, where they are most needed, ensuring that the most critical pathways are hardened before a single line of production code is even written.
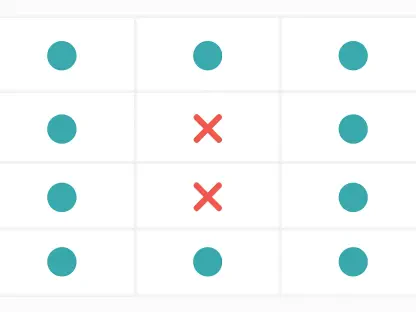
Context-Aware Dependency and Vulnerability Management
One of the most significant hurdles in Java development is the sheer volume of third-party libraries, many of which carry latent vulnerabilities. The risk-driven framework introduces a prioritization rule that multiplies the CVSS score by exposure and business criticality. This formula acknowledges that a critical vulnerability in an offline, internal utility is often less dangerous than a medium-risk vulnerability in an internet-facing authentication component. By focusing on the reachability of a vulnerability—determining if the flawed code is actually executed in the application’s runtime—teams can reduce their remediation workload by up to sixty percent without increasing their risk profile.
Emerging Trends in Proactive Java Protection
The industry is currently moving toward automated reachability analysis, which uses static and dynamic instrumentation to prove whether a vulnerable library function is accessible to an attacker. This innovation moves beyond simple version checking, providing developers with definitive proof of exposure. Furthermore, there is a growing trend toward “Self-Healing” Java runtimes that can automatically apply virtual patches or disable risky code paths during execution. These developments suggest a future where the gap between vulnerability discovery and mitigation is measured in minutes rather than months, fundamentally changing the economics of cyber defense.
Real-World Applications and Sector Deployment
In the financial services sector, where legacy systems often integrate with modern Java-based web portals, this framework has been instrumental in securing the transition from Java 8 to more modern versions. A notable implementation involved a global bank that utilized risk-driven modeling to prioritize the modernization of its SAP-integrated systems. By identifying high-risk ActiveMQ endpoints and obsolete APIs early, the team was able to secure the most vulnerable data pathways first. This targeted strategy allowed them to complete a massive migration with minimal downtime, proving that security can act as a facilitator for digital transformation rather than a hindrance.
Implementation Challenges and Technical Hurdles
Despite its benefits, the transition to a risk-driven model is not without friction. The primary challenge lies in the cultural shift required for developers and security teams to agree on “business criticality” definitions. There is often a technical hurdle in integrating disparate tools—such as static analysis, dependency tracking, and runtime monitoring—into a single source of truth. Regulatory environments also present a barrier, as many compliance frameworks still demand “fix-all” approaches that do not account for risk-based prioritization. Overcoming these obstacles requires a combination of automated orchestration and a top-down commitment to modernizing corporate security policies.
Future Trajectory of Java Enterprise Security
The horizon for Java security points toward a deeper integration of artificial intelligence to predict potential attack vectors before they are exploited. We can expect to see more sophisticated “Security Twins,” where a digital replica of the enterprise architecture is used to simulate attacks and test risk-based responses in a safe environment. As the Java language itself evolves with features like Project Panama and Loom, the security frameworks must also adapt to handle the complexities of high-concurrency and native code integration. This trajectory suggests that security will become increasingly invisible, embedded directly into the compiler and the runtime environment.
Final Assessment and Strategic Key Takeaways
The evaluation of the risk-driven enterprise Java security framework revealed a paradigm shift that successfully balanced defensive rigor with operational agility. It was observed that organizations adopting these principles moved away from the exhaustion of endless vulnerability lists toward a more calculated, impactful strategy. The evidence showed that prioritizing high-exposure assets and utilizing practical threat modeling created a more resilient architecture than traditional, broad-spectrum approaches. Moving forward, stakeholders should invest in automated tools that provide real-time visibility into the reachability of vulnerabilities. Establishing a unified risk language between engineering and executive leadership was found to be the most critical step for long-term success. Ultimately, the framework demonstrated that true security is not found in the absence of risk, but in the intelligent management of it.