Security teams keep patching prompt injections after the damage, but enterprise Java stacks keep sending raw strings into LLMs, and the blast radius keeps growing with every release cycle, which raises a blunt question that this review answers: what changes when prompts are treated like structured API calls instead of open text?
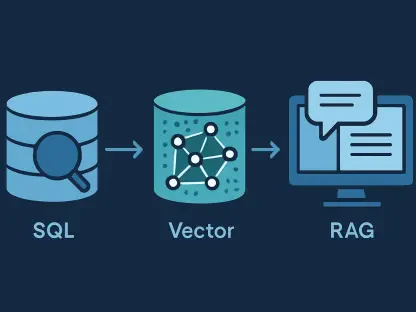
What the AI Query Layer Is and Why It Matters
AI Query Layer (AIQL) reframes LLM integration by outlawing free text as an input type and replacing it with enum-only, schema-validated fields that are audited before any model is invoked. By doing so, it removes the primary channel prompt injection exploits: the shared text buffer where system instructions and user content collide. The claim is simple yet forceful—if the application never accepts arbitrary strings, there is nothing to inject.
This approach responds to the rising tide of injection tactics that mutate faster than blocklists and moderation prompts can keep up. Instead of betting on detection after the fact, AIQL constrains inputs to a deterministic set of choices that can be reviewed, versioned, and reasoned about. In the broader market, it represents a schema-first integration pattern that makes prompts predictable and security controls auditable rather than advisory.
Architecture and Key Components
Enum-Only Schema Model
AIQL schemas are written in YAML and insist that every field is typed as an enum; strings are disallowed and rejected at load time. This yields a finite, closed world of allowed values, transforming prompt construction from freeform concatenation into selection among named intents and attributes. The attack surface shrinks because no unbounded text channel exists for adversarial instructions to ride in on.
The model supports required, optional, and defaulted fields so application flows remain ergonomic without sacrificing guarantees. Defaults provide stability, required flags enforce completeness, and the absence of string types ensures no silent escape hatches reappear later. The result is a contract that security and compliance teams can review like any configuration-driven API.
AIQLEngine Pipeline
The engine operates as a guarded pipeline: applyDefaults, validate, compilePrompt, and client.send. Validation happens before any prompt construction, and failures short-circuit the call so models are never hit with malformed or out-of-policy inputs. This fail-fast behavior does more than save tokens; it hardens the boundary where most ad hoc systems are weakest.
A deliberate separation exists between the raw query map and the compiled prompt. The former never reaches the network boundary; only the compiled, schema-conformant prompt gets transmitted to the provider. This division enables cleaner logging, reproducibility, and defense-in-depth, since audit trails can show both the input choices and the exact prompt produced.
Provider-Agnostic Client Interface
Underneath, a pluggable AIClient abstraction decouples schema logic from model providers. Swapping from Anthropic to OpenAI or a custom inference service is a configuration change, not a refactor. That portability preserves the consistency of validation outcomes and error semantics regardless of backend shifts.
For teams standardizing across multiple business units, this abstraction matters operationally. It supports procurement flexibility, eases cost optimization, and cushions against vendor API churn, all while maintaining the same deterministic request surface and logs.
Configuration and Secret Management
Providers are configured via an external providers.yaml, and API keys are resolved from the environment rather than source code. This separation keeps schemas, provider choices, and runtime secrets isolated, making compliance reviews faster and misconfiguration less likely.
The design aligns with established Java ops practices: treat config as an artifact, keep secrets out of repos, and validate structure on startup. In practice, this reduces both accidental exposure and the risk of subtle, runtime-only drift.
Validation and Error Reporting
AIQL returns deterministic rejection codes such as INVALID_FIELD, INVALID_VALUE, and MISSING_REQUIRED, paired with structured details for logging. That clarity eliminates the guesswork of regex-heavy filters and the ambiguity of model-generated refusals.
Because these outcomes are stable and parseable, they plug cleanly into monitoring stacks. Security teams can aggregate failure patterns, auditors can trace decisions, and developers can debug input issues without re-running costly model calls.
Response Handling and Output Shape
AIQL encourages declaring an expected response shape so downstream parsers know what to anticipate. While inputs are tightly controlled, outputs still require validation since model behavior cannot be fully constrained by upstream structure. The library draws a bright line: it governs what goes in, and applications must still enforce what comes out.
This division of responsibilities keeps the system honest. It avoids suggesting that input determinism alone guarantees end-to-end safety, and it nudges implementers toward schema-aware parsing and safety checks after inference.
Recent Developments and Market Context
Prompt injection moved from novelty to endemic threat, accelerated by open-ended prompting in business workflows. Traditional string-based defenses lag because attackers exploit ambiguity and linguistic variety, not just known bad tokens. As organizations connect LLMs to sensitive data, the tolerance for nondeterminism narrows.
Against this backdrop, typed prompts and schema-first design have gained ground, especially where audit trails matter. The Java ecosystem is catching up with provider-agnostic clients and observability hooks, and AIQL slots neatly into that trend by translating security needs into compile-time and load-time constraints rather than runtime hope.
Real-World Use Cases and Implementations
AIQL fits best where intents are fixed, stakes are high, and reproducibility is non-negotiable. Finance teams running portfolio analysis, healthcare systems triaging claims, legal operations classifying document types, and risk engines summarizing incidents benefit from strict allowlists and visible contracts. In each domain, the ability to review a schema and say “this is the total space of queries” carries governance weight.
Typical patterns include analysis, classification, summarization, and escalation triage. Because the choices are enumerated—intent, asset class, topic, time horizon—the resulting prompts are consistent across runs, aiding both quality control and cost predictability.
Comparative Assessment Against Common Mitigations
Blocklists and Keyword Filters
Filters scan input strings for suspicious tokens, but attackers obfuscate with misspellings, encoding, or multilingual pivots. Maintenance overhead grows without closing gaps, and false positives frustrate users. The shape of the problem remains unbounded.
AI Self-Moderation
Asking the model to refuse malicious input depends on instruction hierarchy winning against adversarial phrasing. That contest is probabilistic, not guaranteed, and fails inconsistently across model versions. It provides guidance, not a guardrail.
Output Filtering
Scanning responses for policy violations treats symptoms after the model has already processed tainted input. This misses subtle instruction hijacks that produce plausible but harmful guidance. It is necessary for defense-in-depth, yet insufficient on its own.
Delimiter Wrapping
Fencing user text with XML or markdown markers helps but is fundamentally advisory; clever prompts can still blur roles or escape delimiters. The approach works until it does not, especially under adversarial testing.
AIQL Enum Validation
By eliminating free-text inputs, AIQL removes the principal injection vector rather than labeling it. This structural constraint yields determinism and auditable change control, turning security from model psychology into input calculus. The cost is reduced flexibility; the benefit is measured reliability.
Summary Comparison
Every mitigation has a place, but only AIQL changes the threat model by design. Filters and wrappers temper risk; enums abolish it on the input side. In regulated settings, that distinction translates into shorter audits, stronger attestations, and fewer late-night incident calls.
Limitations, Risks, and Mitigations
Schema Trust and Governance
Schemas become part of the trusted computing base. If they are altered by an attacker or carelessly expanded, protections erode. Treat schemas like code with versioning, reviews, and access controls, and monitor for drift across environments.
Allowlist Design Quality
Overly broad enumerations reintroduce ambiguity under a different name. Effective schemas prefer narrow, meaningful values that map cleanly to intents. Design workshops with domain experts help strike the right balance between coverage and control.
Accommodating Legitimate Free-Text Needs
Some workflows genuinely need text. AIQL supports mediated patterns where inputs reference pre-approved snippets, retrieval identifiers, or template slots that are filled from trusted corpora. This retains safety while offering a controlled escape valve for nuance.
Output Validation and Parsing
Tight inputs do not absolve output checks. Enforce expected shapes, validate types, and run safety screens where necessary. Consider schema-aware parsers and JSON validation to catch malformed or unexpected responses.
Operational Concerns
Retries, timeouts, and resilience belong in the calling layer, not the core validator. Deterministic inputs can lower token waste and improve cache hits, yet throughput remains gated by provider limits. Plan for backoff strategies, idempotency, and cost controls.
Future Directions and Opportunities
Hybrid Structured and Free-Text Boundaries
Expect safer text channels governed by templates or controlled vocab expansion. The aim is to keep high-entropy input in small, sandboxed pockets with explicit provenance rather than reopening the main gate.
Typed Output Contracts and Schemas
Strengthening response contracts with JSON Schema and end-to-end type safety would close more gaps. This shift would make output parsing as predictable as input validation, further reducing failure modes.
Policy-as-Code and Compliance Tooling
Automated audits, CI checks, and drift detection for schemas can translate governance into repeatable pipelines. Bringing policy-as-code to AI prompts turns reviews from meetings into builds.
Developer Experience and Tooling
IDE plugins, schema linters, and enum auto-suggest would cut friction and prevent misconfigurations. Better tooling makes the secure path the easy path, raising adoption without mandates.
Ecosystem Growth and Providers
Broader client support, on-prem inference, and domain-specific schema packs would extend reach. Portability remains a differentiator as teams balance cost, latency, and data residency.
Formal Methods and Verification
Proving non-interference and compositional guarantees would move AIQL from best practice to verifiable control. Even partial proofs could satisfy strict regulators and critical infrastructure buyers.
Summary and Overall Verdict
AIQL replaced improvisational prompt hygiene with a structural contract: only enumerated, validated inputs reach the model, and everything else is rejected deterministically. The architecture aligned with enterprise Java norms—externalized config, provider abstraction, and machine-parseable errors—while closing the core injection pathway rather than wallpapering it. Trade-offs existed: schemas demanded governance, enumerations required discipline, and outputs still needed validation. Yet the net effect was compelling for fixed-intent workflows where auditability, reproducibility, and portability trumped open-ended flexibility. The decisive verdict favored adopting AIQL as a foundation for production-grade, compliant LLM features in Java, while pairing it with downstream output validation and upstream governance to complete the safety envelope.