

The rapid acceleration of AI's ability to generate functional code has far outpaced the methodologies designed to measure its competence, creating a critical blind spot in the development of next-generation software tools. For years, the industry benchmarked these models by their success in solving
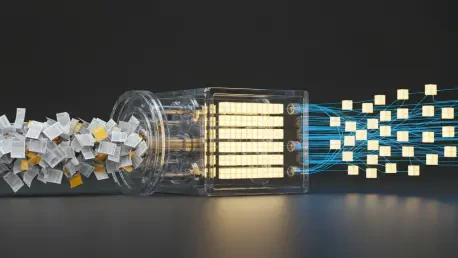
In the rapidly expanding universe of artificial intelligence, the computational cost and complexity of deploying large language models represent a formidable barrier, separating groundbreaking research from real-world application. As organizations race to harness the power of generative AI, the

In the face of escalating climate threats, the island nation of Vanuatu has launched a landmark initiative to fortify its critical transportation infrastructure, moving from a reactive maintenance model to a proactive, data-driven strategy. With a sprawling 2,900-kilometer road network, much of

Our guest today is Vijay Raina, a leading voice on enterprise SaaS technology and software architecture. We're diving deep into the recent announcements from AWS re:Invent to understand the seismic shifts happening for developers. We’ll explore the rise of truly autonomous AI agents capable of

The ever-expanding volume and complexity of telemetry data generated by modern distributed systems present a formidable challenge for developers and operations teams striving to maintain system observability. The Fluent Bit processor represents a significant advancement in telemetry data pipelines,
For years, inefficient code has operated like a silent tax on businesses, a hidden operational expense quietly siphoning funds through wasted cloud resources and underutilized hardware. This once-overlooked form of technical debt, often accepted as a standard cost of doing business, has now been
In the world of application security, threats often evolve faster than defenses. But when OWASP announced a brand-new category for its 2025 Top 10, "Mishandling of Exceptional Conditions," our guest, Vijay Raina, didn't just take note—he took action. In a single weekend, he built a static analysis

Achieving a true Zero Trust security posture on Google Cloud Platform (GCP) requires a fundamental shift away from outdated perimeter-based defenses that have become increasingly ineffective in the modern technological landscape. In today's environment, characterized by distributed microservices,
The rapid and widespread adoption of Application Programming Interfaces (APIs) has fundamentally reshaped modern software development, but this interconnectedness has simultaneously created a sprawling and often unmonitored attack surface that leaves organizations critically vulnerable. In this new
In high-stakes professional domains such as immigration law, regulatory compliance, and healthcare, unchecked language generation from artificial intelligence is not a harmless bug but a significant and costly liability. A single fabricated citation in a visa evaluation can derail a critical
ITCurated uses cookies to personalize your experience on our website. By continuing to use this site, you agree to our Cookie Policy