The shift from large language models as simple chat interfaces to autonomous AI agents represents the most significant transformation in enterprise software since the transition to microservices. For years, the industry struggled with the "stochastic parrot" problem, where models could talk about a

The difference between a flawlessly scaling infrastructure and a catastrophic system collapse often hinges on a single, poorly understood distinction between a reactive tool and an architectural property. Many organizations operating in the current high-stakes cloud environment mistakenly believe
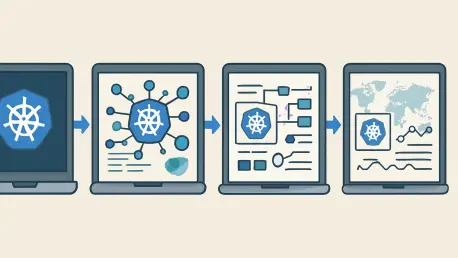
The current technological landscape demonstrates that the days of managing Kubernetes through a single, localized desktop application are rapidly fading into historical obscurity as enterprise requirements evolve. While individual resource browsers once provided a necessary window into the nascent
The structural integrity of a global enterprise often rests upon the invisible scaffolding of its ERP system, yet most organizations treat the transition to S/4HANA as a mere software update rather than the radical architectural reconstruction it truly represents. Moving away from the legacy SAP

Enterprises are finding that the once-celebrated centralized data lake has become a cumbersome liability in the race for generative artificial intelligence dominance. While the early part of the decade focused on sheer volume, the current landscape of 2026 demands precision, context, and agility

The recent disclosure of two maximum-severity vulnerabilities within the Cisco Secure Firewall Management Center represents a watershed moment for enterprise network administrators who rely on centralized orchestration for their defense-in-depth strategies. These flaws, specifically tracked as