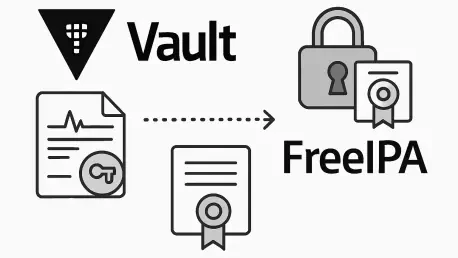
In an era where digital security is paramount, managing public key infrastructure (PKI) has become a critical challenge for organizations, especially those operating in dynamic, cloud-native environments. Gone are the days when a certificate could be placed on a virtual machine and left untouched
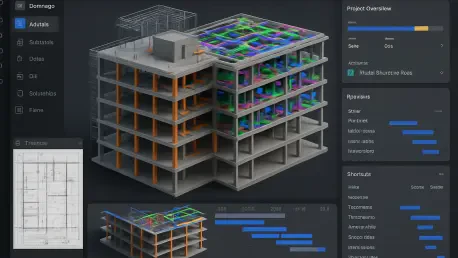
In a landscape where digital innovation is reshaping industries from construction to entertainment, the design software sector has emerged as a powerhouse, particularly in the second quarter of 2024, with Procore Technologies (NYSE: PCOR) carving out a notable position among industry giants. This

In today's fast-evolving digital landscape, managing vast amounts of data within cloud data warehouses has become a critical challenge for organizations aiming to harness actionable insights efficiently. As businesses increasingly rely on cloud-native environments to store and process data, the

What happens when the intricate, time-consuming process of building REST interfaces in the financial sector gets a high-tech makeover? In an industry where every second counts and compliance is paramount, a group of IT architects has turned to Artificial Intelligence, specifically Large Language
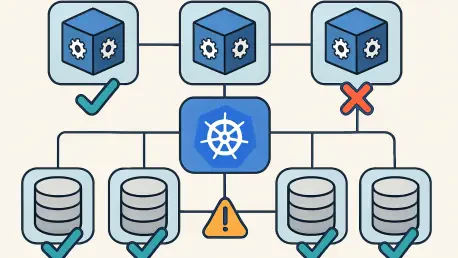
In today’s fast-paced digital landscape, businesses face immense pressure to deliver seamless user experiences, even when systems encounter unexpected failures, and this challenge becomes especially evident during high-stakes scenarios. Consider a situation where an e-commerce platform processes

In the heart of a bustling e-commerce platform, millions of transactions flood through every second, each vying for access to shared inventory data across global data centers. A single misstep in synchronization could mean duplicate orders, frustrated customers, and significant revenue loss. This