When a high-value customer service interaction suddenly dissolves into a blank screen because a security layer decided to revoke a trusted connection without warning, the business cost manifests as immediate operational paralysis. A customer service representative answers a high-priority call, but the Computer Telephony Integration panel remains a blank gray box, severed from the customer’s record. There are no error logs in the application code, the vendor’s servers are running perfectly, and the network is stable, yet the integration has vanished into thin air. This is the reality of Content Security Policy drift—a phenomenon where a security boundary that worked yesterday silently rejects a critical service today.
The core of the problem lies in the fact that security configurations are often treated as static “set and forget” parameters during initial implementation. However, modern enterprise workflows rely on a delicate web of third-party services that are constantly in flux. When a security policy fails, it does not typically offer a helpful warning or a gradual performance degradation. Instead, the browser’s enforcement engine simply terminates the connection, leaving the user with a broken interface and no immediate path toward resolution. This deterministic failure mode makes policy drift one of the most dangerous, yet overlooked, risks in the modern Salesforce ecosystem.
The silent nature of these failures creates a significant diagnostic gap between IT operations and security compliance. Because the rejection happens within the user’s browser rather than on the server, traditional monitoring tools often miss the event entirely. Organizations find themselves in a reactive cycle, where the only indication of a major integration failure is a flood of support tickets from frustrated users. To solve this, technical architects must look beyond the initial setup and understand the dynamic forces that cause a once-valid policy to become obsolete in a live production environment.
The Silent Killer: Why Enterprise Workflows Fail
In the high-stakes environment of a modern contact center, every second of system downtime translates directly into lost revenue and diminished customer trust. The Salesforce Lightning interface acts as the primary cockpit for these operations, housing a variety of embedded tools through frames and specialized components. When the Content Security Policy fails, it acts as a silent killer because it does not trigger the usual alarms associated with server outages or database errors. The application itself is technically “up,” but its ability to communicate with the outside world has been surgically removed by the browser’s own security logic.
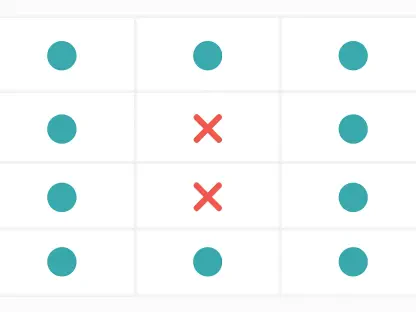
The complexity of these workflows means that a single CSP violation can have a cascading effect across multiple departments. For instance, if a payment gateway frame is blocked due to a policy mismatch, the sales team cannot finalize transactions, the accounting team sees incomplete records, and the customer experience is fundamentally compromised. This is not a failure of the vendor’s API or the Salesforce platform itself, but a failure of the “trust contract” that was established months or years prior. The invisibility of the enforcement mechanism means that teams often waste hours troubleshooting network latency or software bugs before realizing the root cause is a simple header rejection.
Furthermore, the lack of transparency in standard browser enforcement makes it difficult for non-technical stakeholders to understand the severity of the issue. When a global case management system relies on the successful loading of external frames to bind live interactions to customer identities, any disruption to that loading process is catastrophic. The identity chain is broken, and the data remains siloed in the external system, unable to reach the Salesforce records where it is needed most. This disconnect highlights the necessity of treating security boundaries as active components of the application architecture rather than passive background settings.
The Volatility: Navigating the Embedded Boundary
Within the Salesforce Lightning ecosystem, the integration of external services like telephony, payment gateways, and analytics relies on a sophisticated trust chain. This setup assumes that the security perimeter defined during the initial implementation will remain static over time. However, the browser’s enforcement engine evaluates this trust every single time a page renders, making the CSP a volatile runtime dependency. The identity chain, which is the backbone of global case management, relies entirely on the successful loading of these external frames to bind live interactions to specific customer records.
The fallacy of static configuration is perhaps the most dangerous assumption in long-term integration health. Many teams believe that if an integration “worked in the sandbox,” it is ready for permanent production use. In reality, the sandbox environment rarely mirrors the complex, multi-layered security landscape of a live production org, especially when dealing with global CDNs and regional edge routing. The security perimeter must be viewed as a runtime contract that includes four essential pillars: the Lightning Origin, Allowed Frame Origins, the Enforcement Engine, and Redirect Resolution. Each of these components is subject to change, and a shift in any one of them can invalidate the entire contract.
Defining the security boundary as a contract requires a shift in perspective from manual entry to engineering rigor. The “Configured Origin” is the URL a developer enters into the Salesforce setup menu, but the “Resolved Origin” is what the browser actually sees after network redirects and load balancing. In a world where infrastructure is increasingly abstracted, these two values are rarely identical for long. As third-party vendors optimize their delivery networks, they may change the underlying domains used to serve their content, inadvertently tripping the CSP and cutting off the integration without the Salesforce admin ever being notified of the change.
Mechanisms: The Reality of Temporal Drift
Temporal drift occurs when an integration is validated at one point in time but enforced under evolving conditions that were not present during the initial testing phase. As the security landscape matures, the gap between the original settings and current enforcement standards widens, creating an exposure window that leads to deterministic rejections. This drift is not a matter of “if” but “when,” as the underlying technologies that govern web security are in a state of constant advancement. Browser hardening trends represent a primary driver of this phenomenon, with frequent updates from major vendors refining CSP evaluation logic and tightening restrictions to combat emerging threats.
Salesforce seasonal release cycles also play a critical role in the evolution of security enforcement. With three major updates per year, the platform continually refines its internal isolation rules and how it handles third-party frame interactions. A configuration that was perfectly compliant in the Spring release might find itself at odds with new security defaults introduced in the Winter update. Because these updates are mandatory and universal, they can trigger widespread integration failures across an entire organization if the CSP has not been proactively reviewed. The platform’s commitment to security means that the rules are always moving toward a state of higher restriction.
Infrastructure mutation further complicates the landscape by introducing variables that are outside the direct control of the Salesforce administrator. Content Delivery Networks and regional edge routing can change a stable “Configured Origin” into a “Resolved Origin” that the CSP no longer recognizes. For example, a vendor might migrate their assets to a new regional cluster to improve latency, but if that new cluster uses a different subdomain, the existing policy will block the traffic. This highlights the reality that the security boundary is not just a list of domains, but a reflection of the physical and logical infrastructure that supports the integration at any given moment.
Deterministic Engineering: Shifting to Policy as Code
Treating security settings as manual UI configurations is a recipe for inconsistency and human error, particularly in large-scale deployments. To maintain stability, organizations must transition to an “as-code” methodology, transforming the Content Security Policy from an invisible background setting into a versioned, auditable engineering artifact. This starts with the utilization of CspTrustedSite metadata, which allows security boundaries to be represented within the Salesforce metadata framework. By moving these settings into the same repository as the application code, teams can ensure that security is treated with the same level of discipline as any other feature.
Version control and environmental parity are the cornerstones of this new engineering approach. Using Git and modern CI/CD pipelines allows teams to track every change to the policy, providing a clear audit trail of who modified a trusted site and why. It also ensures that the staging and production environments remain in perfect sync, eliminating the “it worked in dev” excuse. When the security policy is part of the deployment package, it is tested and validated alongside the functional code, reducing the likelihood of a configuration mismatch during a release. This alignment between security and development is essential for maintaining a high velocity without sacrificing system integrity.
The implementation of a “headless harness” provides the final layer of defense against policy drift. By using automated testing tools like Puppeteer to simulate real-world browser enforcement during the staging phase, organizations can catch CSP violations before they ever reach a single end-user. These automated validation scripts can be configured to fail the build if any console errors related to security rejections are detected. This turns the security boundary into a formal release gate, ensuring that no integration is deployed unless it has been proven to function within the current enforcement regime. This proactive stance moves the team from a state of constant fire-fighting to one of predictable, deterministic stability.
Observability: Strategies for Long-Term Management
When an integration fails due to a policy rejection, it is rarely a mystery; rather, it is a measurable transition that can be diagnosed with the right data and tools. By logging the state of the security boundary as first-class metadata, teams can move from reactive troubleshooting to a model of proactive management. Long-term boundary observability requires tracking the discrepancy between the configured URLs and the final resolved origins at the time of each transaction. This data allows architects to see exactly how the integration environment is changing over time and to identify potential issues before they result in a total service outage.
Correlating these failures with broader infrastructure events is key to understanding the root causes of drift. By mapping integration outages against vendor CDN updates or Salesforce platform upgrades, teams can identify patterns that suggest a need for policy adjustments. For instance, if multiple integrations fail simultaneously following a browser update, it indicates a change in global enforcement logic that requires a systemic response. Maintaining an “Integration Descriptor Model” is a highly effective way to manage this complexity, as it provides a record of the last validated Salesforce release and compliance status for every embedded surface within the organization.
Maintaining trust integrity is the ultimate goal of these observability strategies. While systems can often survive brief periods of latency or minor bugs, they cannot recover from a severed trust boundary without manual intervention from an administrator. The cost of a broken CSP is not just technical; it is a loss of institutional confidence in the digital workspace. By treating the Content Security Policy as a living, breathing part of the integration architecture, organizations ensure that their critical workflows remain robust in the face of an ever-changing security landscape. The ability to see the boundary clearly is the first step toward controlling it.
The challenges associated with Content Security Policy drift were once viewed as isolated technical hurdles, but they eventually demanded a fundamental shift in how enterprise integrations were governed. Engineers recognized that the security perimeter was not a wall to be built once, but a garden that required constant cultivation and monitoring. The transition toward metadata-driven policies and automated headless testing proved to be the only viable path for maintaining stability in an environment where browser standards and infrastructure evolved weekly. Organizations that adopted these deterministic engineering practices successfully minimized their exposure to silent failures, ensuring that their critical customer-facing tools remained functional across every Salesforce release. By the time the industry matured, the concept of manual CSP configuration had become a relic of a less disciplined era. The lessons learned from managing these volatile boundaries highlighted that the strength of an integration was only as reliable as the trust contract supporting it. Ultimately, the proactive management of the security layer became a core competency for any team operating within the Lightning ecosystem, transforming a potential point of failure into a foundation for resilient, long-term digital innovation.