Modern cybersecurity landscapes have transitioned into a state of perpetual engagement where the boundaries between routine network maintenance and active defense against sophisticated threats have effectively blurred into a single operational challenge for global enterprises. As digital transformation continues to accelerate, the reliance on Application Programming Interfaces has created an expansive attack surface that remains under constant, automated siege. Recent industry data indicates that malicious traffic targeting these critical connection points is no longer a periodic disruption but a permanent fixture of the corporate environment. Between the early months of 2026 and the end of the current cycle, the average frequency of daily attacks per organization effectively doubled, signaling a profound shift in how adversaries approach enterprise infrastructure. This surge reflects a tactical evolution where attackers leverage sophisticated tools to bypass traditional perimeters. Consequently, security teams are now forced to navigate a reality where volume and complexity intersect to threaten the very stability of modern software-driven economies.
The Evolution of Logic-Based API Vulnerabilities
The current threat landscape is increasingly defined by the rise of behavior-based attacks which systematically exploit the underlying logic of application workflows rather than relying on known software bugs or traditional exploit kits. Unlike standard volumetric threats that are easily identified by sudden spikes in traffic, these sophisticated campaigns often mimic legitimate user requests, making them nearly invisible to conventional security monitoring tools. By manipulating the sequence of API calls, adversaries can trick systems into exposing sensitive data or performing unauthorized actions while appearing as authorized traffic. This shift toward logic-based exploitation requires a fundamental change in defensive strategies, moving away from static signatures toward dynamic, context-aware analysis. Enterprises that fail to adapt their monitoring capabilities to account for these subtle behavioral deviations find themselves increasingly vulnerable to silent breaches that can persist for months without detection, as the attackers blend seamlessly into the noise of regular daily operations.
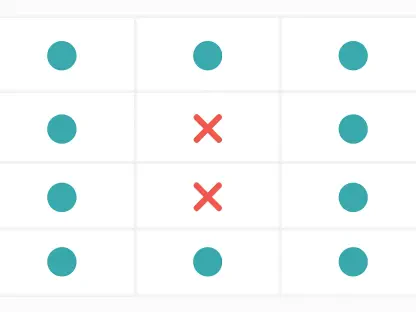
A persistent challenge contributing to this vulnerability is the significant visibility gap that remains prevalent across many large-scale enterprise environments despite the deployment of advanced security suites. While most organizations maintain a functional inventory of their public-facing and internal endpoints, a critical disconnect often exists regarding the specific nature of the data being processed through these channels. Many security teams lack the necessary tools to distinguish which APIs are handling personally identifiable information or high-value financial transactions, creating a strategic blind spot that attackers are eager to exploit. This lack of granular visibility prevents the effective prioritization of security resources, as teams may inadvertently focus on protecting low-risk assets while leaving sensitive data pipelines exposed. Closing this gap necessitates the implementation of automated discovery and classification systems that provide real-time insights into data flows, ensuring that protection measures are accurately aligned with the actual risk profile of each individual application.
Strategic Automation and Multi-Layered Infrastructure Threats
Adversaries are currently undergoing a major strategic shift by moving away from exclusive focus on high-profile data exfiltration toward the systematic degradation of system performance and the inflation of cloud infrastructure costs. By leveraging AI-driven automation, threat actors can now execute large-scale campaigns with minimal financial investment, effectively weaponizing the scalability of modern cloud environments against the organizations that use them. These automated attacks are designed to trigger excessive resource consumption, leading to significant financial strain and operational slowdowns that can be just as damaging as a traditional breach. This “denial of wallet” tactic exploits the elastic nature of cloud services, where automated scaling mechanisms inadvertently increase operational expenditures in response to artificial traffic surges. The ability for attackers to maintain these operations over extended periods without significant overhead has transformed the threat from a series of isolated events into a persistent economic challenge that requires a more robust financial response.
The complexity of these operations is further amplified by the proliferation of sophisticated botnets, such as those known as Aisuru and Kimwolf, which weaponize vast networks of IoT devices and mobile hardware to fuel large-scale Distributed Denial of Service activity. These modern campaigns are notably characterized by their multi-layered approach, frequently targeting Layers 3, 4, and 7 of the networking stack simultaneously within a single, coordinated operation. This technique places immense pressure on both network stability and application-facing systems, making mitigation significantly more difficult for traditional traffic-scrubbing services. The software and SaaS sectors are particularly vulnerable to these tactics because their business models rely entirely on constant availability and low latency for their global user bases. In high-risk regions like the Asia-Pacific area, where web application and API attacks continue to climb into the billions annually, the intersection of botnet automation and multi-layered disruption represents a critical threat that demands a comprehensive defense.
Strengthening Defensive Postures for Operational Resilience
To effectively counter these sophisticated threats, organizations must prioritize the integration of advanced behavioral analytics that can distinguish between legitimate user interactions and malicious automated workflows in real time. This approach involved establishing a baseline of normal application behavior and using machine learning models to identify anomalies that indicated an ongoing attack or reconnaissance effort. Furthermore, the implementation of strict configuration management and continuous testing of API endpoints ensured that security patches were applied and that logic flaws were identified before they could be weaponized. Strategic defense also required a focus on rate limiting and credential stuffing prevention, as these remained common entry points for bot-driven campaigns. By adopting a proactive stance that emphasized visibility and automated response, enterprises created a more resilient architecture capable of absorbing and mitigating the impact of even the most complex multi-layered attacks, ultimately safeguarding both their sensitive data and their broader operational integrity.
The path toward achieving a secure and resilient API ecosystem required a dedicated focus on closing visibility gaps and refining the identification of sensitive data pathways. Successful enterprises recognized that traditional perimeter defenses were no longer sufficient and instead finalized the transition toward context-aware security frameworks. These organizations prioritized the deployment of automated discovery tools and behavioral monitoring systems, which allowed them to effectively mitigate the risks associated with AI-driven botnets and multi-layered infrastructure attacks. By formalizing these advanced defensive measures, security leaders ensured that their infrastructure could withstand the economic and operational pressures exerted by modern adversaries. The focus shifted from mere reaction to the proactive management of the entire application lifecycle, establishing a new standard for digital security. Ultimately, the integration of real-time threat intelligence and robust configuration management provided the necessary foundation for maintaining stability and trust.