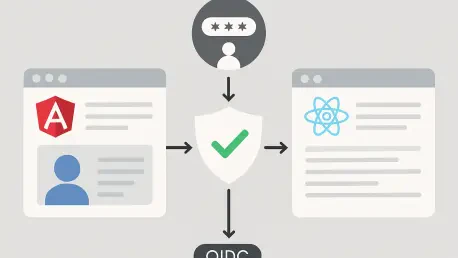
Modern web security has evolved far beyond simple password fields, as developers now grapple with a landscape where user identity must be both portable and impenetrable across diverse cloud environments. When a user clicks a button to sign in using a corporate or social account, they are participating in a sophisticated exchange of digital handshakes facilitated by OpenID Connect. This protocol functions as an identity layer on top of the OAuth 2.0 framework, allowing applications to verify the identity of an end-user based on the authentication performed by an Authorization Server. As single-page applications become the standard for enterprise software, understanding the nuances of this integration in frameworks like Angular and React is no longer optional for the modern developer.
This article explores the specific implementation strategies required to bridge the gap between frontend frameworks and identity providers. We will address the technical hurdles of token management, the shift toward more secure authorization flows, and the practical steps needed to protect client-side routes. By the end of this guide, the reader will have a comprehensive understanding of how to maintain a high security posture while ensuring a seamless user experience.
Key Questions: Exploring OIDC Implementation
Why Is Authorization Code Flow With PKCE the Modern Standard?
The digital landscape has largely moved away from the Implicit Flow, which was once the standard for browser-based applications but suffered from significant security vulnerabilities. Authorization Code Flow with Proof Key for Code Exchange, or PKCE, provides a robust alternative by ensuring that even if an attacker intercepts the authorization code, they cannot exchange it for an access token without a secret code verifier. This mechanism is particularly vital for single-page applications because they are “public clients” that cannot safely store a client secret in the browser source code without exposing it to the world.
Moreover, leading identity providers like Okta, Auth0, and Keycloak have shifted their default recommendations to favor this flow to align with OAuth 2.1 specifications. By utilizing a dynamically generated high-entropy cryptographic random string, the application creates a challenge that the identity provider validates during the token exchange. This adds a critical layer of protection against authorization code injection and interception attacks, making it the most resilient choice for developers who prioritize data integrity and user privacy.
How Is OIDC Configured Within an Angular Environment?
Integrating OIDC into an Angular ecosystem typically involves leveraging a mature library like angular-oaut##-oidc, which handles the complexities of the discovery document and silent refresh. The configuration begins with defining an authentication object that specifies the issuer URL, the client identifier, and the necessary scopes such as openid, profile, and email. Because Angular applications are often highly structured, this configuration is best managed through a dedicated authentication service that can be initialized during the application bootstrap process. Using an APP_INITIALIZER ensures that the authentication state is determined before the user even sees the first page, preventing flickering or unauthorized access to sensitive views.
Furthermore, the implementation extends into the routing module where developers must protect specific paths using functional guards. These guards check the validity of the access token and initiate the login flow if the user is not authenticated. By configuring a resource server interceptor within the OAuth module, the application can automatically attach the Bearer token to outgoing HTTP requests. This seamless integration allows developers to focus on building features while the library manages the heavy lifting of token storage in memory and the background renewal of sessions through hidden iframes or refresh tokens.
What Does the Implementation Look Like for React Applications?
React developers often favor the react-oidc-context library, which is built upon the robust oidc-client-ts foundation to provide a more idiomatic, hook-based approach. The setup usually involves wrapping the entire application in an AuthProvider component that injects the authentication context into the component tree. This allows any child component to access the user’s identity and authentication status through a simple hook call. Unlike the more rigid structure of Angular, React provides the flexibility to create custom higher-order components or wrapper components to handle route protection, offering a more declarative way to manage protected content.
In addition to context management, handling the authentication callback in React requires a dedicated route that processes the URL parameters returned by the identity provider. While the library often handles this automatically, a specialized callback component can provide a better user experience by displaying a loading spinner while the token exchange completes. This approach ensures that the application state remains synchronized with the identity provider. Developers can then utilize custom hooks to fetch data from secured APIs, ensuring that the necessary authorization headers are appended only when a valid token is present in the application state.
What Are the Risks Associated With Token Storage?
One of the most debated topics in frontend security is where to store sensitive tokens once they are retrieved from the identity provider. Storing access tokens in localStorage or sessionStorage is a common practice due to its simplicity, yet it exposes the application to Cross-Site Scripting vulnerabilities. If a malicious script runs on the page, it can easily scrape these storage areas and exfiltrate the tokens. To mitigate this, many security experts recommend keeping tokens in memory only, which means the token is lost on a page refresh but remains shielded from common script-based attacks.
To provide a more permanent yet secure solution, some organizations implement the Backend for Frontend pattern, where the frontend never actually sees the token. Instead, a server-side proxy handles the OIDC flow and sets a secure, httpOnly cookie that the browser automatically sends with API requests. This effectively removes the token from the reach of JavaScript entirely. While this adds complexity to the architecture, it is often required for high-stakes environments like financial services or healthcare, where the cost of a compromised session is exceptionally high.
Summary: Essential Takeaways
The integration of OpenID Connect into Angular and React applications solidified the security architecture of modern web platforms by standardizing how identity is handled. Developers realized that the combination of Authorization Code Flow and PKCE offered the best balance between security and developer experience, effectively neutralizing many common attack vectors. The use of specialized libraries simplified the management of complex tasks like discovery document validation and silent token refreshes.
Maintaining a secure application required constant vigilance regarding token storage and the configuration of redirect URIs. It became clear that the security of a frontend application is only as strong as its weakest link, often found in the way tokens are handled in the browser. Using memory-based storage or moving toward a BFF architecture emerged as the preferred methods for protecting user sessions. These strategies provided a resilient foundation for building applications that users can trust with their most sensitive data.
Final Thoughts: Navigating Future Security Challenges
Successfully implementing OIDC was only the first step in a broader journey toward building truly secure digital experiences. As authentication technologies continue to advance, the focus moved toward reducing the reliance on long-lived sessions and embracing more granular access control. Developers found that staying updated with the latest security best practices was essential, as the tools and protocols governing identity are constantly being refined to counter new threats.
Those who mastered these authentication patterns were better prepared to handle the complexities of multi-tenant environments and federated identity systems. The shift toward more secure, browser-native authentication methods suggested a future where the friction of signing in would continue to decrease even as security increased. Every developer should have assessed their current authentication implementation to ensure it met modern standards, as the cost of technical debt in security is far higher than in any other area of software development.