The rapid expansion of autonomous digital entities has fundamentally rewritten the rules of enterprise security, forcing a shift from simple password management to a comprehensive identity framework. In the current landscape starting in 2026, organizations find themselves managing a hybrid workforce where human employees share credentials and access points with sophisticated AI agents. This transformation necessitates a dual-layered defense strategy that can verify biological users while simultaneously monitoring the programmatic behaviors of machine identities. Traditional security perimeters, which once relied on static human logins, are increasingly insufficient against the speed and complexity of automated workflows. By introducing the Unified Access platform and the Users API for Partners, 1Password has addressed these emerging challenges, providing a centralized mechanism to oversee every digital actor within a network. This shift reflects a broader industry movement toward holistic identity security, ensuring that the integration of AI does not become a liability for modern cloud-integrated enterprises.
Centralizing Control: Bridging the Gap Between Human and Machine Identities
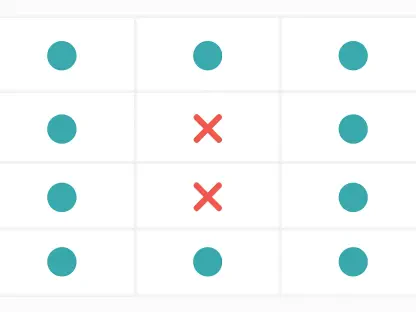
Mapping the Hidden Landscape of Shadow IdentitiesThe proliferation of non-human identities, or NHIs, often occurs without the explicit knowledge of IT departments, leading to a dangerous expansion of the organizational attack surface. These shadow identities frequently emerge when developers deploy automated scripts or AI agents to streamline cloud-integrated workflows, often leaving exposed credentials in local environments or browser caches. The Unified Access platform solves this by implementing an aggressive discovery model that scans development environments and endpoints to identify these hidden risks. By surface-leveling these obscured access points, the system allows security teams to gain a transparent view of every entity capable of interacting with sensitive data. This proactive identification is the first step in reclaiming control over a decentralized digital footprint, ensuring that no autonomous agent operates in a vacuum. Transitioning these found credentials into a centralized vault allows for the application of uniform security policies across the entire organization.
Establishing Rigorous Audit Trails for Autonomous EntitiesEffective security in 2026 requires more than just finding credentials; it demands a rigorous auditing process that treats machine actions with the same scrutiny as human logins. Once identities are secured within the Unified Access ecosystem, the platform maintains a continuous monitoring cycle that records how both biological and digital actors navigate enterprise systems. This creates a detailed audit trail that is essential for maintaining regulatory compliance and detecting anomalous behavioral patterns in real-time. For instance, if an AI agent suddenly begins chaining together tools or accessing databases outside its typical operational parameters, the system flags this deviation immediately. This level of oversight ensures that the autonomy granted to AI does not bypass the oversight required for enterprise-grade security. By merging these disparate identity types into a single administrative view, organizations can finally eliminate the silos that previously allowed attackers to move laterally through poorly monitored machine accounts.
Automating Responses: Enhancing Resilience Through the Users API
Accelerating Remediation Through Automated Identity ResponseWhile visibility provides the foundation for security, the ability to respond to threats at machine speed is what truly defines modern identity resilience. The Users API for Partners introduces a mechanism for automated identity response, allowing external security tools to communicate directly with 1Password’s management layer. In a scenario where an intrusion detection system identifies a compromised account, the API can trigger an immediate suspension of access without requiring manual intervention from a human analyst. This capability is critical when dealing with automated attacks that can exfiltrate massive amounts of data in seconds. By shrinking the window between detection and containment, the API transforms the password manager from a passive storage unit into an active participant in the incident response lifecycle. This integration enables security operations centers to embed access control changes into their broader playbooks, ensuring that every identity—human or AI—can be neutralized instantly if it presents a verifiable risk.
Securing Management Channels With Modern Authorization StandardsTechnical robustness is the core of this automated response system, utilizing modern authorization frameworks like OAuth 2.0 and scoped tokens to maintain a high security posture. These standards replace the traditional reliance on long-lived, static credentials for management tasks, which were often a primary target for exploitation themselves. By using temporary, limited-scope tokens, the API ensures that the communication between 1Password and its partners is as secure as the data it protects. This approach facilitates a move from one-time authentication at the start of a session toward a model of real-time, continuous authorization. In this environment, every action taken by an AI agent or a human user is treated as a distinct event that requires validated permissions. As credentials evolve into active control points, the system gains the flexibility to adjust access rights dynamically based on the current threat level or specific task requirements. This granular level of control is necessary for managing the complex, multi-step workflows typical of current AI-driven business processes.
Forward Thinking: Practical Steps Toward Identity Integrity
Strategizing the Integration of Human and Machine ControlsOrganizations looking to secure their digital ecosystem must prioritize the unification of their identity management strategies to avoid the pitfalls of fragmented security. The first practical step involves auditing all current AI integrations to determine which agents possess autonomous access to sensitive internal databases or third-party APIs. Once these entities are mapped, security leaders should integrate them into a centralized platform like Unified Access to ensure that machine secrets are rotation-compliant and encrypted. Furthermore, companies should leverage the Users API to build automated kill switches within their security operations centers, allowing for the instant revocation of permissions during a suspected breach. This shift requires a cultural change where non-human identities are treated with the same level of risk assessment as high-privilege human accounts. By standardizing these protocols now, businesses can build a scalable foundation that accommodates future technological expansions without sacrificing the integrity of their data or the trust of their users.
Reflecting on the Success of Unified Identity FrameworksThe implementation of a holistic identity framework successfully bridged the gap between human oversight and machine autonomy, creating a more resilient enterprise environment. This transition moved the industry away from reactive security toward a proactive stance where every digital interaction was verifiable and controlled in real-time. Security teams that adopted these unified platforms realized a significant reduction in the time required to neutralize credential-based threats, as the automation handled the initial containment phases. Looking ahead, the focus shifted toward refining the behavioral analytics that govern AI agents, ensuring that their operational logic remained aligned with corporate security policies. The integration of advanced API management and centralized discovery tools proved that managing a diverse workforce did not have to result in increased complexity or vulnerability. Ultimately, the move toward continuous identity security established a new standard for trust in a world where biological and artificial intelligence must coexist and collaborate within the same secure parameters.