As an expert in enterprise SaaS technology and software architecture, Vijay Raina has spent years navigating the intricate plumbing of the internet. With a deep background in designing resilient cloud infrastructures, he has witnessed firsthand how a simple misunderstanding of core protocols can lead to hours of unnecessary downtime. Today, he joins us to demystify DNS propagation—a process often treated as a waiting game but which, in reality, is a precisely controllable mechanism. By shifting our perspective from “waiting for the internet to update” to “managing cache expiration,” Vijay illustrates how network administrators can execute seamless migrations and site launches with surgical precision.
The following conversation explores the technical relationship between authoritative servers and recursive resolvers, the hidden dangers of negative caching during new launches, and the strategic use of Time-to-Live (TTL) values to achieve zero-downtime migrations.
Many professionals still operate under the belief that DNS changes inherently require 24 to 48 hours to propagate globally. How does the relationship between authoritative servers and recursive resolvers dictate this timeline, and what specific TTL values should be set to reduce this window to just a few minutes?
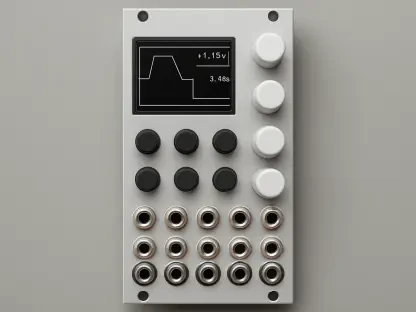
The “24-hour rule” is actually a persistent myth born from a misunderstanding of how caching layers interact. When you update a record at a provider like name.com, that change is live on their authoritative nameservers—like ns1 through ns4—almost instantly. The bottleneck occurs at the recursive resolvers, which are the intermediary servers run by ISPs or public providers like Google’s 8.8.8.8. These resolvers don’t constantly check for updates; they store a copy of your record based on the Time-to-Live (TTL) value you’ve set. If your TTL is 86,400 seconds, a resolver will wait exactly 24 hours before asking the authoritative server for a fresh IP. To compress this window to just a few minutes, you must manually lower your A record’s TTL to 300 seconds. This instructs every resolver on the planet to check back every 5 minutes, effectively shrinking a day-long wait into a brief coffee break.
New site launches are often disrupted by negative caching when users visit a domain before records are fully configured. What technical mechanisms cause these “domain not found” responses to persist in a resolver’s cache, and what specific sequence of steps ensures a clean launch without users hitting stale error pages?
Negative caching is a silent launch-killer that occurs when a resolver receives an NXDOMAIN response, meaning the domain doesn’t exist yet. This negative answer is cached based on the SOA record’s minimum TTL field, which can often be set to several hours by default. If a user hits your URL before you’ve pointed it to a server, their ISP’s resolver remembers that the site is “missing” and won’t look again for a long time, even after you’ve updated your A records. To avoid this, the sequence of operations is critical: you must fully configure every DNS record in your dashboard before announcing the site or sharing the link. By populating the records first, you ensure that the very first query a resolver makes returns a valid IP address rather than a cached “not found” error that could lock users out for half a day.
Executing a server migration without downtime requires keeping both old and new infrastructure active simultaneously. How should an administrator time the reduction of TTL values before the move, and what is the practical process for verifying that traffic has fully transitioned before decommissioning the legacy hardware?
Timing is the most vital element of a zero-downtime move, and you have to start the process 48 hours before you even touch your server. If your current TTL is 86,400 seconds, you must change it to 300 seconds and then wait at least 24 to 48 hours to ensure all old, long-term caches worldwide have expired. Once that window passes, you update the IP to the new server while keeping the old server running; this is the “dual-serving” phase where some users hit the old IP and some hit the new one. To verify the transition, you shouldn’t just refresh a browser; you need to use the dig command to query specific resolvers like @8.8.8.8 or @1.1.1.1 and check the “ANSWER SECTION.” Only when your server logs show zero traffic hitting the old hardware and all public resolvers return the new IP should you finally decommission the legacy infrastructure.
While a 300-second TTL offers agility, it increases the query volume and load on authoritative nameservers. In what specific scenarios is it better to maintain a 24-hour TTL, and how do you determine the “sweet spot” for a production environment that balances performance with the need for emergency rollbacks?
There is definitely a trade-off between agility and overhead, though for most modern sites, the extra query load of a short TTL is negligible. However, you should stick to a high TTL of 86,400 seconds for stable, static infrastructure where changes are rare, as this improves response speed for users and provides better resilience against DDoS attacks by keeping records cached longer. For a standard production environment, the “sweet spot” is usually 3,600 seconds, or one hour. This provides a balanced middle ground: you aren’t hammering nameservers every few minutes, but if a disaster strikes, you can initiate a rollback and know that the majority of the world will see the fix within 60 minutes. I generally only drop to 300 seconds during active maintenance windows or when setting up high-availability failover systems.
Relying on a local browser refresh is often misleading when verifying whether a DNS change has reached a global audience. Which command-line tools or public resolvers provide the most accurate picture of propagation, and what specific sections of a “dig” trace should an engineer analyze to find where a record is stuck?
A browser is a terrible verification tool because it has its own internal cache, often layered on top of the OS cache. Instead, an engineer should use the dig command with the +trace flag, which reveals the entire delegation path from the root nameservers down to the TLD and finally your authoritative servers. When analyzing a trace, look at the final “ANSWER SECTION” provided by different public resolvers like Google (8.8.8.8) or Cloudflare (1.1.1.1). If you see a mix of old and new IPs across these resolvers, you know you are still in the transition window. For a broader view, web-based tools like whatsmydns.net are excellent for sensory confirmation, as they show you a map of how the record is resolving across 20 or more global locations simultaneously, proving that your change hasn’t just reached your local city but the entire world.
Managing DNS becomes more complex when dealing with apex domains or email infrastructure. Why are CNAME records restricted at the root level of a domain, and how does the built-in retry logic of MX records change the way you approach a mail server migration compared to a standard A record update?
The restriction on CNAMEs at the apex—meaning example.com without the www—is a technical limitation defined in RFC 1034, because a CNAME cannot coexist with other record types like SOA or NS that must exist at the root. This forces us to use A records or specialized ALIAS records at the apex level. When it comes to MX records for email, the strategy is similar to A records regarding TTL reduction, but we have an extra safety net. Most mail servers have a built-in retry logic; if a server tries to deliver mail during the few minutes a record is updating and fails, it won’t just delete the email—it will queue it and try again later. This makes email migrations slightly more forgiving than web traffic, though you should still lower your MX TTL to 300 seconds to keep that window of inconsistency as narrow as possible.
What is your forecast for the future of DNS management and propagation?
I believe we are moving toward a “Real-Time DNS” era where the concept of a 24-hour propagation delay will become an antique curiosity of the past. As more companies adopt Infrastructure-as-Code and automated API-driven deployments, we’re seeing a shift where TTLs are dynamically adjusted by scripts rather than humans. We will see wider adoption of protocols that allow for even faster updates and more intelligent recursive resolvers that can receive “push” notifications from authoritative servers when a change occurs. My forecast is that within the next few years, the standard minimum TTL will drop even further, and the “propagation window” will be measured in seconds globally, making DNS-based load balancing and instant failover the baseline expectation for even the smallest web projects.